NTLM relay attack detection
Learn how to detect NTLM relay attacks in part four of a special series on critical Active Directory (AD) attack detections & misconfigurations.
Table of Contents
Welcome to part four of a special series on detecting Active Directory attacks & misconfigurations. Each blog post dives deep into identifying, detecting, and mitigating a dangerous AD vulnerability.
And the best part?
You’ll get a free AD-focused Sherlock to practice the defensive techniques you learn!
The attack methods and misconfigurations we cover will include:
Let’s get started!
NTLM relay attacks explained
Windows New Technology LAN Manager (NTLM) is the name of a set of Active Directory protocols that provide authentication in the network. To ensure backward compatibility, NTLM is used mainly on systems that do not support Kerberos authentication.
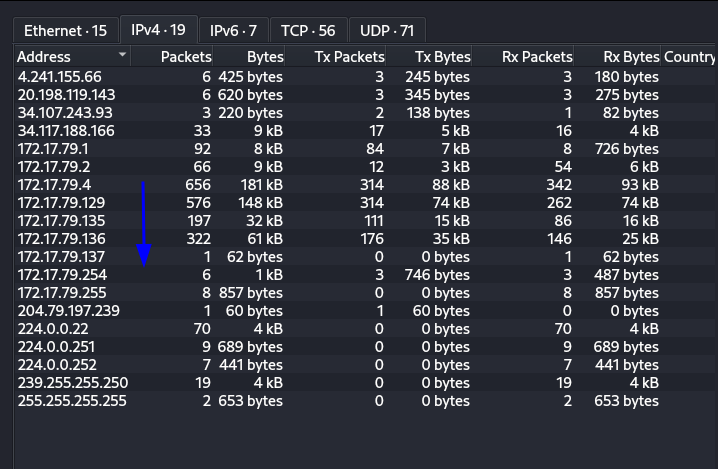
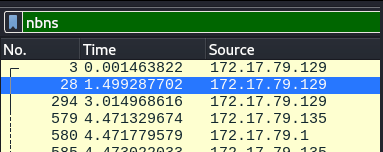
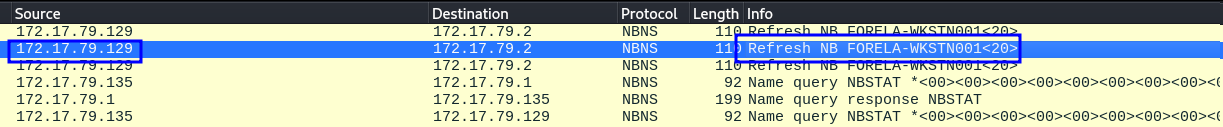
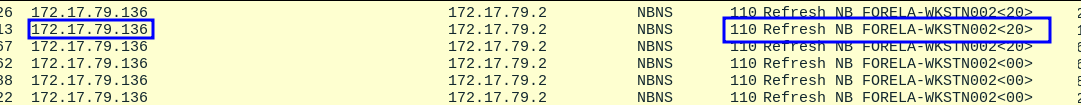
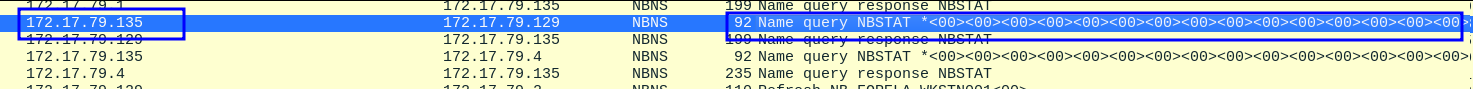
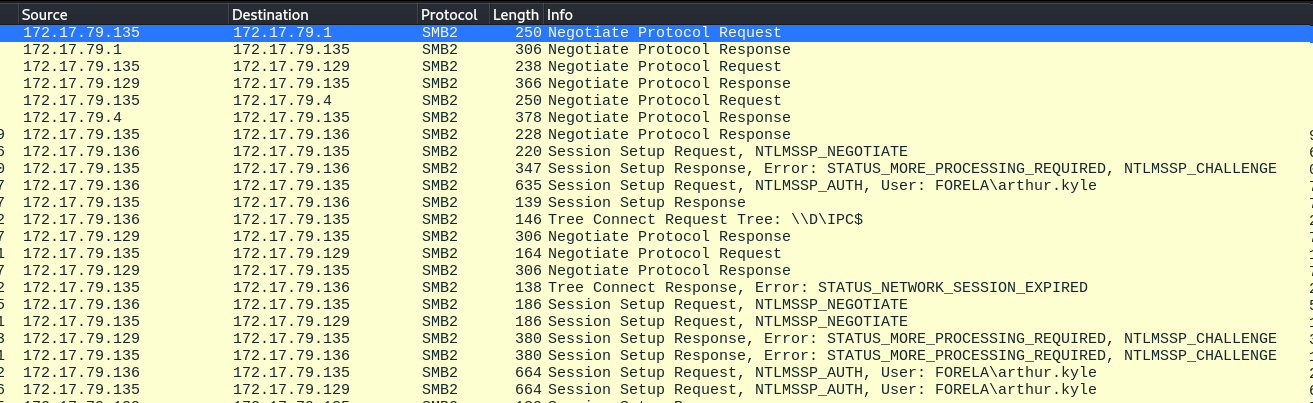
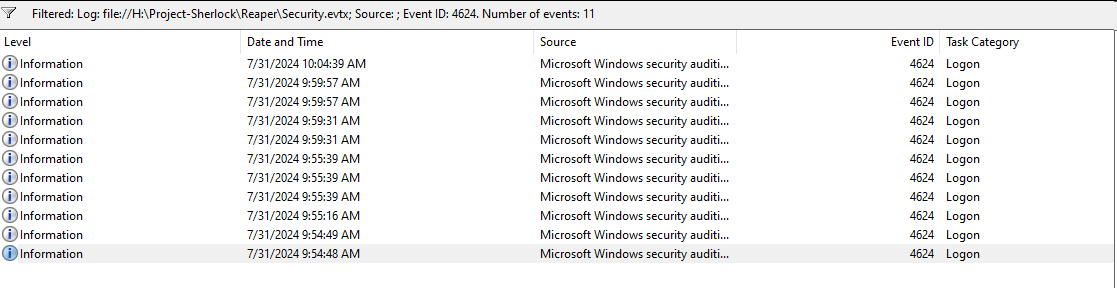
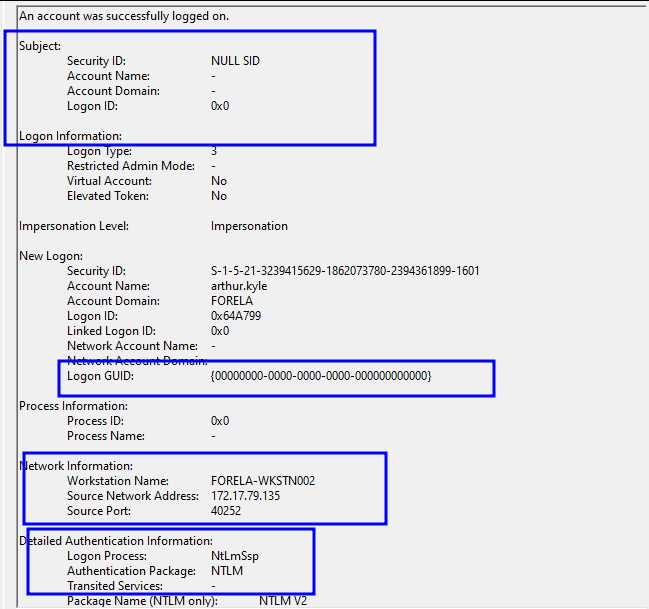
When an attacker intercepts network traffic with an LLMNR poisoning attack, they can further attempt to relay the intercepted event to authenticate themselves to a particular service on behalf of the victim.
This is known as an NTLM relay attack. NTLM relay attacks are possible because the NTLM itself does not provide session security.
Impacket's ntlmrelayx is one of the most commonly used tools that can be leveraged to perform this attack.