A step-by-step guide to writing incident response reports (free template inside)
Discover how to write an incident response report, including an incident reporting template, and a step-by-step reporting process for analysts.
Table of Contents
What is an incident response report?
In cybersecurity, the question isn't whether a security incident will transpire, but rather when it will occur. This is why we require incident response reports to act as a conduit between the identification and remediation of threats.
It serves to archive past incidents, providing an invaluable source of lessons learned from previous mistakes. The learnings can be seamlessly integrated into a broader strategy for preempting and mitigating future threats.
Essentially, an incident response report encompasses the process by which an organization handles a breach. It aims to quickly identify an attack, minimize damage, contain, and remediate the cause to reduce the risk of future incidents.
Incident response report template (+ example)
Why are incident response reports important?
Incident Response (IR) reports are the true narrative of a cybersecurity incident's handling capturing the good, the bad, and the ugly. When accurately written, they serve as a critical platform for reflection and adjustment, spotlighting gaps in processes, people, and technology.
The real power of these reports lies in their ability to turn hindsight into foresight, allowing teams and organizations to rectify issues before they escalate into more significant threats.
Sabastian Hague (sebh24), Defensive Content Lead, Hack The Box
Incident response plans are critical as they help limit and mitigate a security breach's impact. This helps manage an organization’s financial and reputational damage while providing a blueprint for future incidents.
As a result, cybersecurity teams can consistently respond to attacks.
Writing effective incident response reports means striking a balance between detail and accessibility. A good report should be understandable to both technical and non-technical audiences.
A well-organized incident report is a clarifying tool for stakeholders across various functions, including legal departments ensuring regulatory compliance, executive management assessing risk profiles, and CFOs evaluating financial repercussions.
This clarity benefits the overall incident response process:
-
Improved response: Consistent incident response reports enable teams to learn how to spot the early signs of an attack, helping faster retention and recovery.
-
Early threat mitigation: Speed up forensic analysis, minimize the event duration, and any potential negative impacts.
-
Regulatory compliance: Many regulatory and certification bodies (such as the PCI DSS) require organizations to have an incident response plan.
💡 Recommended read: Our top 5 DFIR labs for beginner analysts (to get good fast)
Learn how security incident reporting works

Our Academy module on Security Incident Reporting teaches teams everything they need to know about documenting and reporting an incident.
-
Explore the art of identifying and classifying security incidents.
-
Understand the systematic process of incident documentation.
-
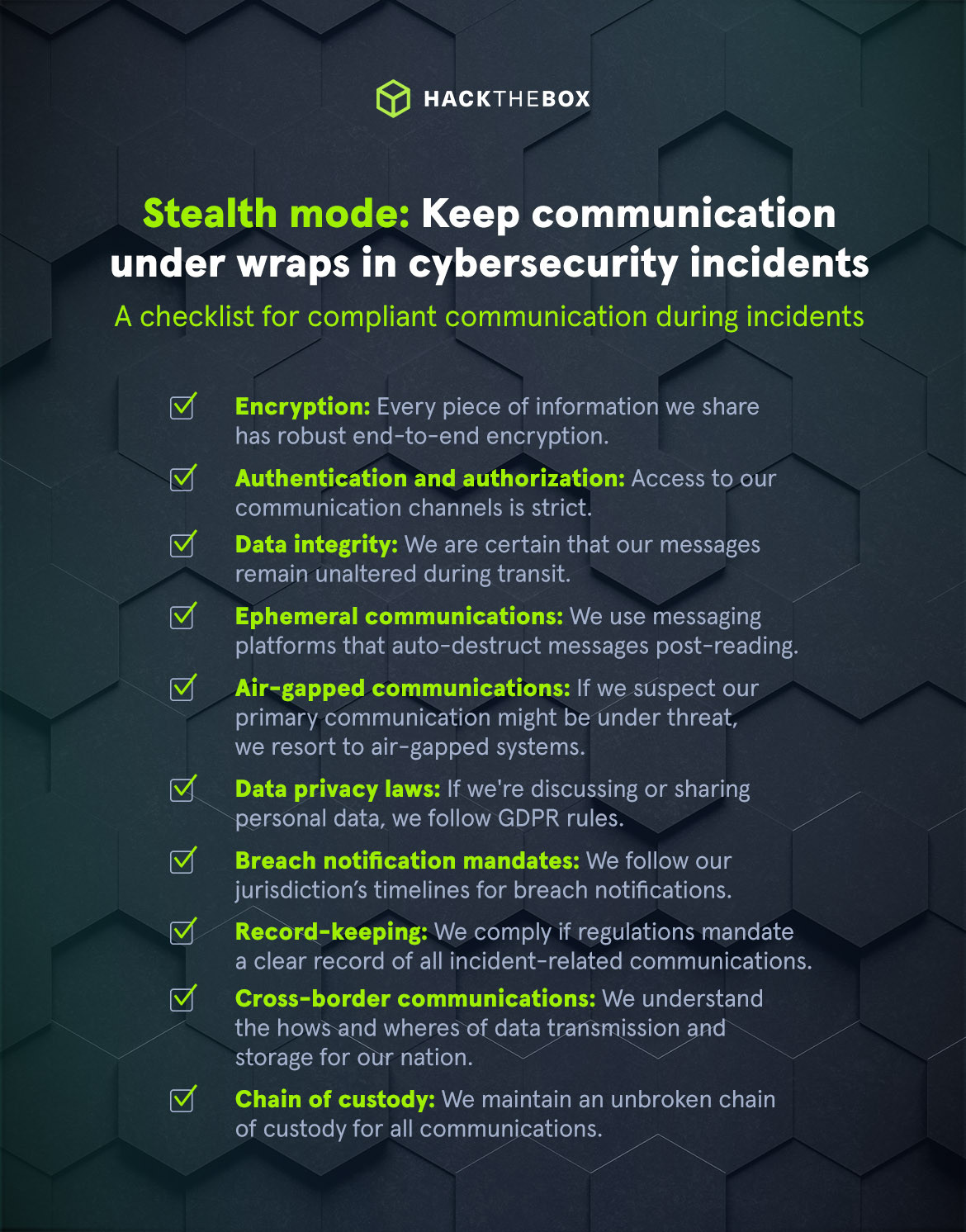
Perfect communication strategies during incidents.
-
Dive into the critical components of a detailed incident report.
-
Analyze a real-world incident report following best practices.
Incident identification and categorization
Organizations are threatened by many different attacks. So, a systematic approach to identifying and classifying security incidents is required.
How can we quickly identify security incidents? These are the three main sources:
|
Source |
Description |
|
Security systems |
Some excellent sources for identification include IDS/IPS, EDR/XDR, SIEM tools, or even basic anti-virus alerts and NetFlow data. |
|
Human observations |
Users may notice and report suspicious activities, unusual emails, or systems behaving abnormally. |
|
Third-party notifications |
Partners, vendors, or even customers might inform organizations about any vulnerabilities or breaches they are experiencing. |
Once an incident has been identified, it must quickly be categorized as this will impact the prioritization and allocation of appropriate resources.
Common incident types include:
-
Malware: Malicious software encompassing viruses, worms, and ransomware.
-
Phishing: Attempts to gather sensitive information, predominantly via email.
-
DDoS attacks: Deliberate attempts to inundate a system or network, thereby disrupting its regular functionality.
-
Unauthorized access: Incidents where unauthorized entities gain access to systems or data.
-
Data leakage: Exposure of confidential data, both within and outside the organizational perimeter.
-
Physical breach: Unauthorized physical access to secure locations.
Now that the nature of the incident has been categorized, individuals will be able to refer to incident response plans and past reports to understand how to react.
💡Get our full incident response template for free.
But what about prioritization? We can classify incidents with the following severity levels:
-
Critical (P1): Imminent threats that jeopardize core business functionalities or sensitive data, requiring immediate intervention.
-
High (P2): Threats to business operations that, while not immediately detrimental, are of elevated priority.
-
Medium (P3): Incidents that, although not posing an immediate threat to business operations, warrant timely attention.
-
Low (P4): Trivial incidents or routine anomalies that can be managed within standard operational workflows.
Incident reporting process
A solid incident reporting process will serve as a cohesive framework to identify, mitigate, retain, and remediate security breaches.
|
Author Bio: Sabastian Hague (sebh24), Defensive Content Lead, Hack The Box Sabastian Hague is a seasoned cybersecurity professional with over eight years of experience in the field. After serving in the Royal Air Force as a specialist in all things SOC, he went on to work for Vodafone's global CERT team before taking on a role as a senior security consultant with SpiderLabs and working on numerous high-profile incidents. He is now the Defensive Content Lead at Hack The Box. Seb has numerous industry certifications, including GIAC Certified Detection Analyst (GCDA), GIAC Continuous Monitoring Certification (GMON), GIAC Certified Incident Handler (GCIH), GIAC Certified Intrusion Analyst, Offensive Security Certified Professional (OSCP), Blue Team Level 1 (BTL1), Blue Team Level 2 (BTL2), Cybereason Threat Hunter (CCTH). |