5 steps to implement cybersecurity reskilling (& close talent gaps)
Cybersecurity leaders can reskill their existing talent into security roles to close skill gaps, retain their best employees, and develop a culture of learning.
Table of Contents
CISOs, managers, and team leaders are under immense pressure to adapt and innovate. They're tasked with finding creative solutions to the ongoing talent shortages that plague the industry.
Amidst these challenges lies a golden opportunity: reskilling initiatives.
Reskilling is about tapping into existing talent within your organization and building formidable cybersecurity professionals from the ground up.
Not only does reskilling help combat cybersecurity talent shortages, but it also keeps teams engaged, retains people you know and trust, offers new career opportunities, and develops a culture of learning within an organization.
The result? A better security posture for your company and a cybersecurity team that’s constantly adapting to threats.
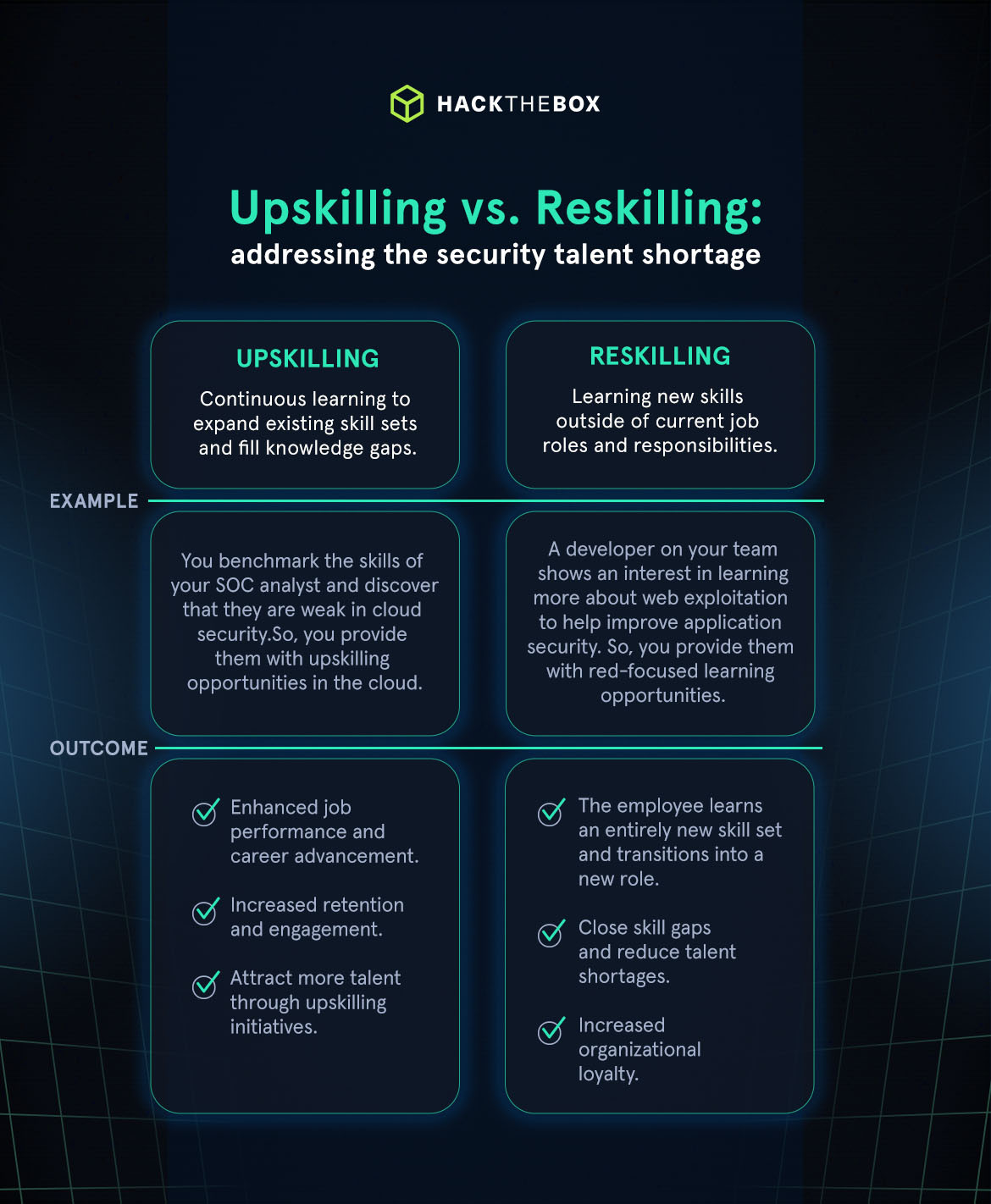
Upskilling vs. reskilling: what’s the difference?
Upskilling and reskilling your team members both help to retain employees, shrink skills gaps, and attract new talent to your organization.
However, there is a difference between the two, especially when it comes to desired outcomes.
Upskilling = linear career progression
💡An employee undertakes continuous learning to expand their existing skill set and fill any knowledge gaps.
💭Example: You benchmark the skills of your SOC analyst and discover that they are weak in cloud security. So, you provide them with upskilling opportunities in the cloud, enabling them to excel in their role while bolstering your organization’s security.
🎯Outcome: The employee has enhanced job performance and advances in their career. This leads to increased retention and engagement, with the chance to attract more talent through upskilling initiatives.
Reskilling = lateral movement to new roles
💡An employee learns new skills outside of their current job role and responsibilities.
💭Example: A developer on your team shows an interest in learning more about secure coding practices to help improve application security. This could translate into them eventually joining your security team.
🎯Outcome: The employee learns an entirely new skill set and transitions into a new role, helping to close skill gaps and reduce talent shortages. This leads to increased loyalty to your organization as you offer employees opportunities to grow into and out of their roles.
The benefits of reskilling
Reskilling enables organizations to fill talent shortages with existing employees. It’s a win-win as 75% of professionals we surveyed prioritize learning new skills over earning higher salaries, meaning reskilling benefits both employees and organizations.
Reskilling an existing IT employee into a cybersecurity role, for example, will often cost a fraction of the price of hiring from the market. Research shows that businesses can save up to £49,100 per reskilled worker when nurturing existing talent rather than hiring externally.
And the savings will only continue as your security posture improves with a growing security team. Employees will want to stay with your organization as you offer them opportunities to shape their careers in ways that are most meaningful for them.
This hugely boosts retention and keeps employees loyal, maintaining a strong team you trust and can depend on.
Reskilling embeds a culture of lifelong learning into your organization, helping with recruitment, retention, and internal rotation of roles.
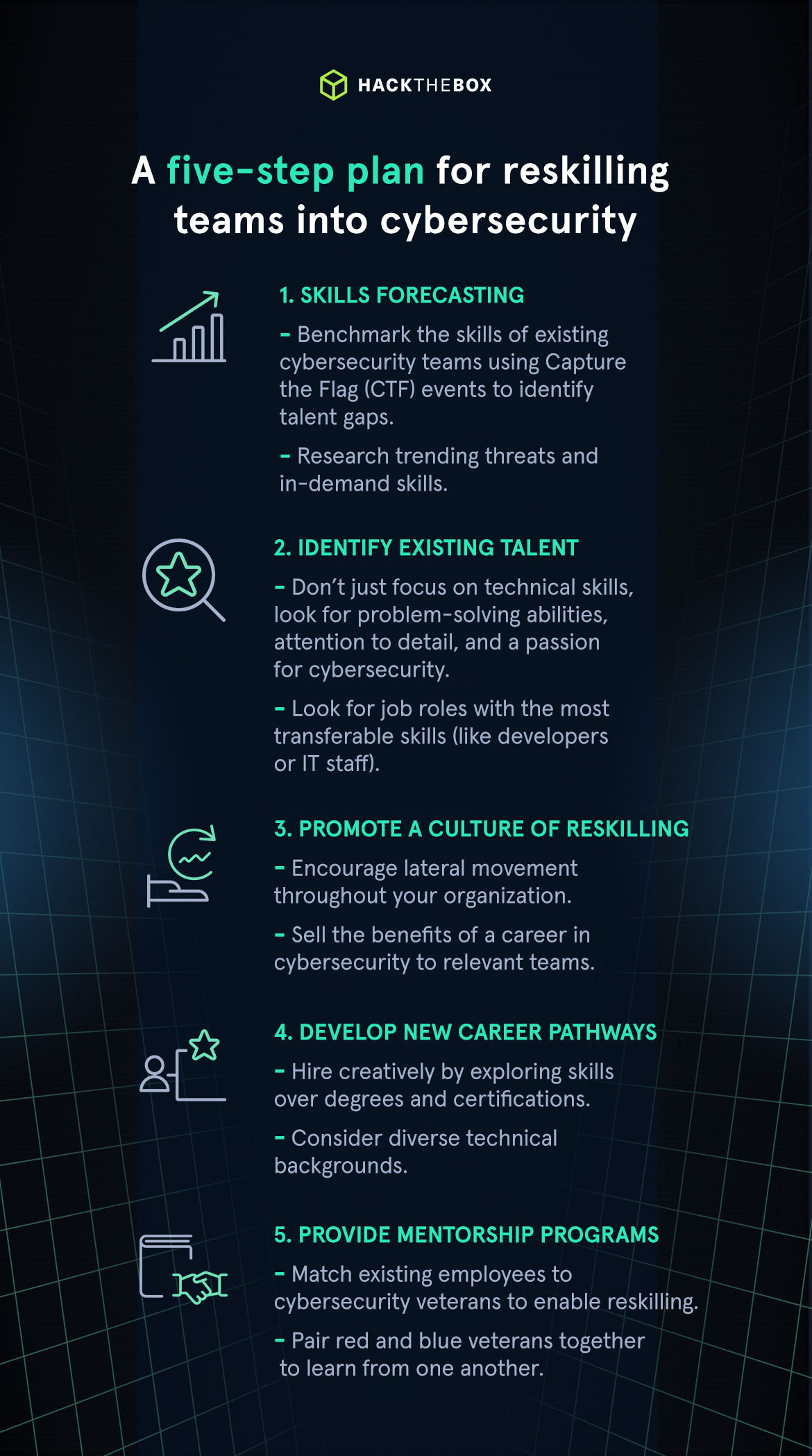
5 steps to reskill teams into cybersecurity roles
5. Provide mentorship programs
Establishing a mentorship program is a proven formula to help reskill employees in the cybersecurity field. A seasoned security mentor can offer career direction, share knowledge, and help foster new connections.
This also provides benefits to the mentor, enabling them to grow their leadership and training skills.
Mentorship can even support existing cybersecurity professionals looking to reskill into specialist domains.
For example, a SOC analyst might mentor a penetration tester, teaching them how to defend Active Directory (AD) against common vulnerabilities, for instance.
This purple team training may look like this:
An organization could perform an exercise where the red team begins an Active Directory related attack within the internal network to see at what threshold the attack tactics are discovered and even blocked.
Once discovered, the red team can move on to attack a different portion of the network, trying to remain as stealthy as possible until the blue team discovers them once again (or not at all).
Afterward, the purple team would facilitate knowledge sharing between the red and blue teams. This way, the red team will be able to adjust their techniques to attempt to better evade detection during future exercises.
Ben Rollin (mrb3n), Head of Information Security at Hack The Box
Our Sherlocks Labs facilitate purple team upskilling with defensive and offensive versions of Machines for the full 360 learning experience:
|
Sherlocks |
Offensive |
|
There’s been a potential security breach within Forela's internal network. It’s your job to investigate, putting your digital forensics and network security skills to the test. |
Exploit an unauthenticated arbitrary file read vulnerability, gaining full administrative access to the machine. |
|
A critical alert has been raised over a newly implemented Apache Superset setup. You need to investigate and confirm the presence of any compromise. |
Test your web application skills as you attempt to exploit a vulnerability in Apache Superset. |
|
You have been tasked with the analysis of artifacts from a potentially compromised GitLab server. |
Explore how you can exploit and gain a foothold in a GitLab server. |
By encouraging mentorship for employees looking to reskill in cybersecurity, you’ll cultivate a supportive environment where teams feel empowered to seek guidance to advance their careers.
The result? More engaged employees, a stronger cybersecurity team, and reduced levels of risk.
Reskill for the future of cybersecurity
Reskilling not only saves time and money in the hiring process but also creates cybersecurity professionals who are passionate and loyal to their organizations.
Why not launch your own reskilling initiative? Hack The Box can help with our beginner-friendly content, defined job role paths, and certifications on Academy.
|
Starting role |
HTB certification training |
Reskilled role |
|
IT support |
|
|
|
Developer |
|
|
|
IT engineers |
|
Cybersecurity engineer |
|
Forecasting and strategic planners |
Threat hunter/threat intelligence analyst |
|
Dan Magnotta (Mags22), HTB Federal Business Development & Capture Manager, Hack The Box Dan Magnotta is an accomplished professional in cybersecurity and intelligence operations with more than a decade of experience in the military and private sectors. His career began with dedicated service to the U.S Department of Defense, where he played critical roles in the U.S. European Command and U.S. Special Operations Command Europe, contributing significantly to cutting-edge cyber strategies. In addition to his civilian role, he serves as an LCDR in the U.S. Navy Reserve, showcasing his leadership and dedication as an Executive Officer for a Navy Reserve Unit. His expertise in cybersecurity, operational analysis, and strategic planning is extensive. At Hack The Box, he tailors solutions to meet the unique requirements of government agencies and organizations worldwide, leveraging his deep understanding of both military and civilian cybersecurity needs. |